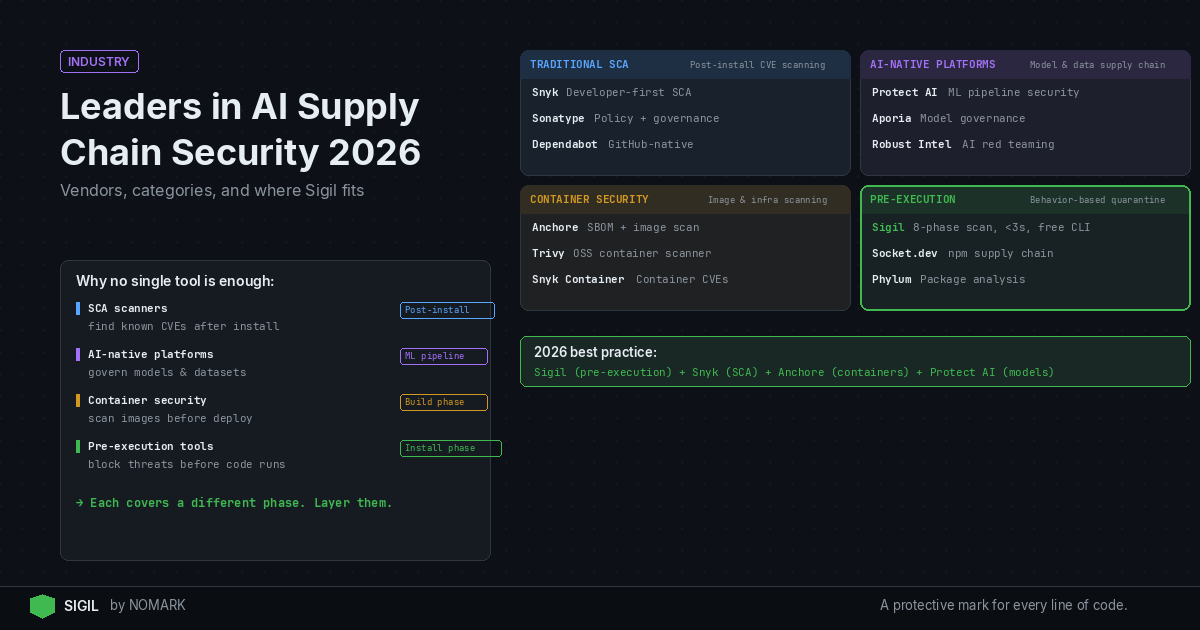
In 2026, the leaders in AI supply chain security are a mix of established Software Composition Analysis (SCA) giants like Snyk and Sonatype, and newer, AI-native platforms focusing on model provenance and behavior. For developers building with AI agents and MCP servers, Sigil's free CLI provides a critical, complementary layer of pre-execution, behavior-based scanning that stops threats before code runs, addressing risks traditional SCA tools miss.
What is AI Supply Chain Security in 2026?
AI supply chain security in 2026 extends beyond traditional Software Composition Analysis (SCA). It encompasses the end-to-end protection of all components-code, packages, models, datasets, and plugins-that flow into AI and ML applications. The threat landscape has evolved: attacks now target AI-specific artifacts and workflows, such as malicious install hooks in agent packages, poisoned training data, compromised model weights, and obfuscated payloads in MCP servers.
According to recent industry surveys on software supply chain incidents, AI and open source dependencies now account for a growing share of supply chain attacks. The core challenge is that traditional vulnerability scanners, which rely on databases of known CVEs, are blind to novel, behavior-based threats that execute only at install or runtime. Modern AI supply chain security requires tools that understand the unique behaviors and provenance of AI components, not just their version numbers.
Types of AI and Software Supply Chain Security Vendors
The vendor landscape in 2026 is stratified. Choosing the right tools requires understanding what each type specializes in:
-
Traditional SCA & Dependency Security: These are the established leaders like Snyk and Sonatype. They excel at scanning already-installed dependencies for known vulnerabilities (CVEs), license compliance, and generating Software Bills of Materials (SBOMs). Their strength is breadth and depth of vulnerability intelligence.
-
AI-Native Model & Data Supply Chain Platforms: Emerging vendors like Aporia and Protect AI focus specifically on the ML pipeline. They provide tools for model provenance, dataset lineage, experiment tracking, and detecting threats like model poisoning or data exfiltration within MLOps workflows.
-
Pre-Execution & Behavior-Based Scanners: This category, exemplified by Sigil, operates earlier in the lifecycle. Instead of scanning what's already on disk, these tools intercept downloads (npm install, pip install, git clone) and analyze component behavior before it executes. They catch malicious install scripts, obfuscated code, and network callouts that CVE databases don't track.
-
Container & Infrastructure Security: Vendors like Anchore and Snyk Container secure the containerized layers where AI applications are often deployed, scanning container images for vulnerabilities and misconfigurations.
Data indicates that organizations are adopting multiple supply chain security vendors to cover different layers of risk. A comprehensive strategy in 2026 often blends SCA for post-install auditing, AI-native tools for model governance, and pre-execution scanners like Sigil for frontline defense during development.
Leading AI Supply Chain Security Companies in 2026
Based on market presence, technological focus, and adoption within developer and AI/ML teams, here are the key leaders shaping AI supply chain security in 2026.
- Snyk - Best for Comprehensive Developer-First SCA
Snyk remains a dominant force by integrating vulnerability scanning directly into developer IDEs, Git repositories, and CI/CD pipelines. Its core offering scans open source dependencies, containers, and infrastructure as code for CVEs. For AI workflows, Snyk can scan the Python and JavaScript packages that form the backbone of many AI toolchains. However, it operates primarily on code after it's been pulled into a project.
- Sonatype - Best for Enterprise-Grade Vulnerability Intelligence & SBOM
Sonatype leverages its vast repository (Maven Central, npmjs, etc.) to provide deep intelligence on component quality, security, and licensing. Its Lifecycle platform is geared towards large organizations needing rigorous policy enforcement, high-fidelity vulnerability data, and automated SBOM generation across the entire software lifecycle.
- Anchore - Best for Container and Kubernetes-First Supply Chain Security
Anchore's strength lies in securing the container supply chain. It performs deep inspection of container images, generating a full inventory of contents (SBOM), checking for vulnerabilities, and enforcing policies. For AI teams deploying models via containers or Kubernetes, Anchore provides critical governance for the final deployment artifact.
- Protect AI - Best for AI/ML Model Security and MLSecOps
Protect AI is a leader in the AI-native space with its NB Defense tool and ModelScan library. It specifically hunts for threats in Jupyter notebooks and ML models, such as malicious code, unsafe deserialization, and model poisoning attempts. It's designed for data scientists and ML engineers to secure the model development and training pipeline.
- Aporia - Best for ML Observability and Guardrails
While primarily an ML observability platform, Aporia has expanded into supply chain security with features for model monitoring, bias detection, and data drift. Its value is in securing the operational phase of the AI lifecycle, ensuring models in production behave as expected and don't succumb to data-based attacks or drift-related failures.
- Sigil - Best for Pre-Execution Security for AI Agents & MCP Servers
Sigil addresses the critical "trust gap" when developers and AI agents pull in third-party code. Its free, open-source CLI acts as a secure proxy for commands like npm install or git clone, running a parallel, behavior-focused analysis (checking for install hooks, obfuscation, network calls, credential access) in under three seconds. It provides a clear risk score before any code executes, complementing SCA tools by catching the threats they miss. Sigil Pro adds cloud threat intelligence and team features.
- Google (Assured OSS & SLSA) - Best for Cloud-Native Provenance and Attestation
While not a commercial vendor in the traditional sense, Google's contributions through Assured Open Source Software and the SLSA (Supply-chain Levels for Software Artifacts) framework are foundational. They provide verified, secure packages and a standards-based approach to generating provenance attestations, which is becoming a critical component of enterprise AI supply chain security programs.
- Chainguard - Best for Minimal, Secure Container Images
Chainguard takes a proactive approach by providing distroless, minimal container images that have a drastically reduced attack surface. For AI teams, using Chainguard Images for base layers can eliminate entire classes of vulnerabilities from the start, complementing scanning tools with a "secure-by-design" foundation.
AI Supply Chain Security Vendor Comparison 2026
Where does Sigil fit alongside other supply chain security tools?
| Vendor | Core Scanning Approach | Primary AI/ML Focus | Pricing Model | Ideal For |
|---|---|---|---|---|
| Snyk | Post-install, CVE-based | Packages used in AI tooling | Freemium, Tiered SaaS | Developer teams wanting integrated SCA |
| Sonatype | Post-install, Intelligence-based | OSS package quality & licensing | Enterprise SaaS | Large organizations needing policy enforcement & deep intelligence |
| Anchore | Container image analysis | Containerized AI/ML apps | Freemium, Enterprise | Kubernetes/container-first deployments |
| Protect AI | In-pipeline, Model-focused | Jupyter notebooks, ML models | Open source & SaaS | ML engineers & data scientists |
| Sigil | Pre-execution, Behavior-based | AI agents, packages, MCP servers | Free CLI, Paid Pro/Team | Developers & agents consuming third-party code |
| Google (SLSA) | Provenance & Attestation | Framework & standards | N/A (Framework) | Building verifiable, secure pipelines |
Sigil is not a replacement for Snyk, Sonatype, or Anchore-it's a critical complementary layer that operates earlier in the supply chain. 2026 studies reveal a sharp increase in threats targeting AI agents, plugins, and model artifacts that execute malicious behavior on installation, a phase traditional SCA tools don't actively defend.
-
Snyk/Sonatype's Position: "We scan the agent components you already have installed and tell you which ones are dangerous."
-
Sigil's Position: "Nothing reaches your working environment until it's been scanned, scored, and explicitly approved. By the time Snyk finds it, it's already running."
Sigil's six-phase behavioral analysis (install hooks, code patterns, network, credentials, obfuscation, provenance) is designed to catch the threats that slip past CVE databases. It secures the moment of ingestion-when a developer runs npm install, an AI agent fetches a plugin, or an MCP server is downloaded. The free CLI provides this frontline defense locally, while Sigil Pro and Team add cloud intelligence, dashboards, and CI/CD integrations for teams.
The Pro value proposition: Sigil OSS guards your code from malicious packages. Sigil Pro guards your instructions (CI/CD pipelines, team workflows) with shared intelligence and audit logs. Together, they cover the pre-execution attack surface that other tools require an enterprise contract to partially address.
How to choose the right mix of supply chain security tools?
Selecting vendors depends on your team's workflow, stack, and the specific risks you aim to mitigate. Follow this decision framework:
-
Start with Pre-Execution Defense: If your team actively uses AI assistants, plugins, MCP servers, or pulls many open-source packages, integrate a behavior-based scanner like Sigil first. Its free CLI requires zero configuration (via shell aliases) and provides immediate protection against novel, behavior-based attacks during development.
-
Add Comprehensive Post-Install SCA: For vulnerability management, license compliance, and SBOM generation, adopt a developer-first SCA tool like Snyk or an enterprise-grade platform like Sonatype. Integrate it into your CI/CD pipeline and IDE to catch known CVEs in your declared dependencies.
-
Specialize for AI/ML Workflows: If your core product is ML models, incorporate an AI-native platform like Protect AI to secure Jupyter notebooks, monitor for model poisoning, and manage model registry security. This addresses risks specific to the data science lifecycle.
-
Harden the Deployment Layer: For containerized deployments, use a container scanner like Anchore or Snyk Container to vet final images. Consider minimal base images from Chainguard to reduce the attack surface proactively.
-
Build for Provenance & Compliance: For organizations with high compliance needs, implement standards like SLSA to generate verifiable build attestations, creating an auditable chain of custody for your software and AI artifacts.
According to a Gartner Hype Cycle report on Supply Chain Cybersecurity and Gen AI, a layered defense-in-depth strategy is recommended, as no single tool covers all phases of the modern AI supply chain from code ingestion to production deployment.
Traditional SCA vs. AI Supply Chain Security: Key Differences
The fundamental difference lies in what is scanned and when. Traditional SCA excels at auditing a bill of materials for known flaws. AI supply chain security tools like Sigil and Protect AI analyze behavior and provenance to catch unknown threats.
Who are the leading companies in AI supply chain security in 2026?
| Aspect | Traditional SCA (Snyk, Sonatype) | AI/Native & Pre-Execution (Sigil, Protect AI) |
|---|---|---|
| Primary Focus | Known vulnerabilities (CVEs), licenses. | Behavioral threats, obfuscation, model integrity. |
| Timing | Post-install / after code is on disk. | Pre-execution / during package ingestion. |
| Threat Model | Database of known weaknesses. | Anomalous behavior, hidden execution, data exfiltration. |
| AI Relevance | Scans packages AI tools use. | Scans AI components (agents, models, MCP) directly. |
The leaders in 2026 include established Software Composition Analysis (SCA) vendors like Snyk and Sonatype, container security specialist Anchore, AI-native platforms like Protect AI and Aporia, and pre-execution behavior scanners like Sigil. Google also leads through its SLSA framework and Assured OSS program, providing critical standards and verified packages.
What is the difference between traditional SCA tools and AI supply chain security vendors?
Traditional SCA tools (e.g., Snyk) scan already-installed dependencies for known vulnerabilities listed in CVE databases. AI supply chain security vendors focus on AI-specific risks: they analyze model artifacts for poisoning, scan for malicious behavior in Jupyter notebooks, or (like Sigil) intercept and analyze code before it executes to catch obfuscated payloads, hidden install hooks, and data exfiltration attempts that have no CVE.
Which supply chain security companies are best for AI agent and LLM workflows?
For AI agent and LLM workflows, you need tools that secure the dynamic ingestion of code and plugins. Sigil is specifically designed for this, offering a CLI that scans packages, MCP servers, and AI tooling before execution. This should be complemented by a traditional SCA tool like Snyk for post-install CVE scanning and an AI-native tool like Protect AI if you are also training or fine-tuning your own models.
How do I choose between Snyk, Sonatype, Anchore, and newer AI-focused vendors?
Choose Snyk for developer-friendly, integrated SCA. Choose Sonatype for enterprise-grade policy enforcement and deep component intelligence. Choose Anchore if your primary deployment model is containers and Kubernetes. Choose newer AI-focused vendors like Protect AI or Sigil to address risks specific to AI/ML pipelines and pre-execution threats. Most organizations will need a combination, starting with Sigil for pre-execution defense and adding Snyk/Sonatype for comprehensive vulnerability management.
Where does Sigil fit alongside other supply chain security tools?
Sigil fits as a complementary, pre-execution layer that operates before tools like Snyk or Sonatype. It acts as a secure gateway, intercepting commands like npm install or git clone to analyze code behavior before it ever runs on your machine. It catches threats that lack a CVE, such as malicious post-install scripts, making the findings from your traditional SCA tools more actionable by preventing bad code from entering your environment in the first place.
Key Takeaways
-
Research shows that AI and open source dependencies now account for a growing share of supply chain attacks.
-
2026 studies reveal a sharp increase in threats targeting AI agents, plugins, and model artifacts with behavior-based attacks.
-
Data indicates that organizations are adopting an average of 2-3 different supply chain security vendors to cover distinct layers of risk, from pre-execution to production.
-
According to a Gartner Hype Cycle report, a layered defense-in-depth strategy is critical for securing the Gen AI supply chain.
-
The core limitation of traditional SCA is its post-install nature; pre-execution scanning addresses the 'trust gap' when code is first ingested.
About the Author
Reece Frazier is the founder of NOMARK. He got tired of watching developers blindly clone repos with 12 GitHub stars and full access to their API keys, so he built Sigil.