Nexus Repository and JFrog Artifactory manage and proxy artifacts, offering storage, access control, and limited vulnerability scanning. Sigil is fundamentally different: it sits in front of these tools, quarantining and behavior-scanning code, packages, and AI tooling before execution. Together, they form a complete secure pipeline-repositories handle distribution and known CVEs, while Sigil actively blocks hidden install hooks, data exfiltration, and obfuscated payloads that traditional scanners miss.
What Nexus Repository and Artifactory Actually Do
Nexus Repository (by Sonatype) and JFrog Artifactory are artifact repository managers. Their primary functions are centralized storage, proxying, and lifecycle management for software packages and dependencies.
Core Capabilities:
-
Universal Repository: Host and proxy packages from npm, PyPI, Maven, Docker, and more.
-
Access Control & Governance: Define who can push, pull, or delete artifacts.
-
CI/CD Integration: Serve as a single source of truth for build outputs and dependencies.
-
Basic Vulnerability Scanning: Both integrate with scanners (like Nexus IQ or JFrog Xray) to identify known CVEs in stored artifacts based on dependency metadata.
Think of them as secure, internal mirrors of public registries and a vault for your own build artifacts. According to Sonatype Help documentation, their performance data and usage metrics are critical for managing enterprise-scale deployments.
Where Traditional Repositories Fall Short on Behavior Threats
While essential for managing artifacts, Nexus and Artifactory have a critical blind spot: they primarily scan what is stored, not what the code does when it runs. This gap is exploited by modern supply chain attacks.
The Execution Gap:
-
Install Hooks: Malicious code in
setup.py,postinstallscripts, or MCP server setup can execute immediately upon download or install, before any human review. -
Behavior-Only Threats: Code that performs credential harvesting, outbound data exfiltration, or cryptocurrency mining may have no known CVEs and thus evade traditional scanners.
-
Obfuscation: Payloads hidden via
eval(base64.b64decode(...))or other dynamic techniques are invisible to static analysis of the artifact file.
Research shows that attackers increasingly target these build and install phases. Data indicates that supply chain attacks abusing npm and PyPI install hooks have grown significantly year over year, a trend expected to continue into 2026.
How Sigil Adds Pre-Execution Quarantine to Your Workflow
Sigil addresses the execution gap directly. It is an open-source CLI that intercepts code before it runs on your machine, performing a fast, parallel behavior analysis.
How It Works: You replace commands like git clone, npm install, or pip install with sigil clone or sigil install. Sigil then:
-
Quarantines the code in a secure container.
-
Analyzes Behavior across six phases: install hooks, code patterns, network/exfiltration attempts, credential access, obfuscation, and provenance.
-
Returns a Verdict in under three seconds with a clear risk score, allowing you to block or proceed.
This creates a safety checkpoint before code reaches your local environment or CI/CD pipeline, complementing your artifact repository's storage and CVE scanning.
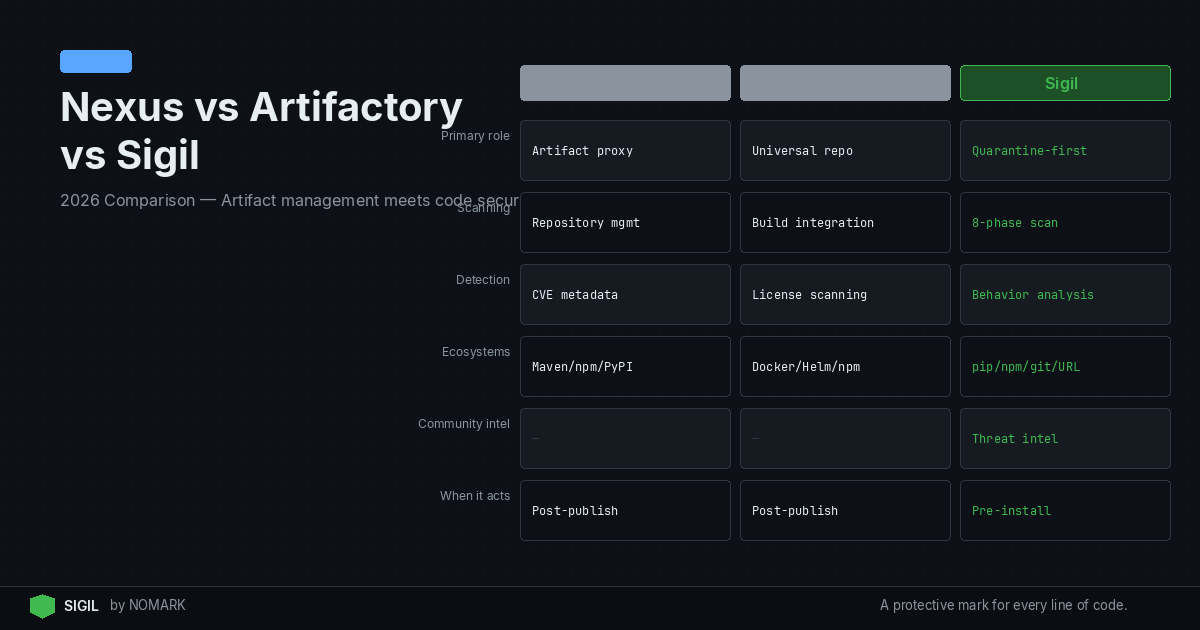
Feature Comparison: Nexus vs Artifactory vs Sigil (2026)
Nexus Pros and Cons
| Feature | Sonatype Nexus | JFrog Artifactory | Sigil |
|---|---|---|---|
| Primary Role | Artifact Repository Manager | Artifact Repository Manager | Pre-Execution Code Quarantine & Scanner |
| Core Function | Store, proxy, manage artifacts | Store, proxy, manage artifacts | Intercept and analyze code behavior before execution |
| Key Threat Detection | Known CVEs (via Nexus IQ) | Known CVEs (via JFrog Xray) | Behavioral threats: install hooks, exfiltration, obfuscation, credential access |
| Scanning Trigger | On artifact storage/request | On artifact storage/request | On code download/install command (e.g., git clone, npm install) |
| Typical Integration Point | CI/CD pipeline, developer pull | CI/CD pipeline, developer pull | Developer shell, CI/CD script, IDE (VS Code, JetBrains) |
| Deployment Model | Self-hosted or Cloud | Self-hosted or Cloud | Local CLI, Self-hosted (air-gapped), Cloud (Pro/Team) |
| License Model | Commercial (Pro) / Open Source | Commercial / Open Source | Open Source Core (Apache 2.0) / Commercial Pro & Team tiers |
| Ideal For | Managing package dependencies & build outputs at scale | Managing package dependencies & build outputs at scale | Securing AI agent code, MCP servers, and open-source packages from behavioral malware |
Pros:
-
Mature & Stable: Long-standing solution with extensive documentation and community.
-
Strong Java/Maven Focus: Excellent native support for Maven repositories.
-
Open Source Version: Free OSS version available for basic repository management.
-
Integrated Security (IQ): Powerful software composition analysis (SCA) for license compliance and known vulnerabilities when paired with Nexus IQ.
Cons:
-
Complexity: Can be complex to configure and maintain at scale.
-
Blind to Runtime Behavior: Does not analyze what code does during installation or execution.
-
UI/UX: Often cited as less modern compared to some competitors.
Artifactory Pros and Cons
Pros:
-
Extensive Protocol Support: Universally supports virtually every package format.
-
High Performance & Scalability: Designed for large, enterprise-scale deployments.
-
Integrated DevOps Platform: Tight integration with JFrog Pipelines and Xray for a full CI/CD security suite.
-
Cloud-Native Offering: Robust SaaS option (JFrog Cloud).
Cons:
-
Cost: Can be expensive, especially for the full platform with Xray.
-
Resource Intensive: Requires significant infrastructure for self-hosted instances.
-
Blind to Runtime Behavior: Like Nexus, it scans artifacts, not execution behavior.
Sigil Pros and Cons
Pros:
-
Pre-Execution Safety: Unique ability to quarantine and scan code before it runs, closing the critical execution gap.
-
Fast & Local: Analysis completes in seconds, works fully offline with zero telemetry.
-
Catches Behavioral Threats: Detects malware that CVE scanners miss (hidden hooks, exfiltration, obfuscation).
-
Developer-First: Zero-config CLI, shell aliases, and IDE plugins fit into existing workflows.
-
Open Source Core: Full transparency under Apache 2.0; auditable and modifiable.
Cons:
-
Not a Repository: Does not replace Nexus/Artifactory; you still need an artifact manager.
-
Newer Ecosystem: Less mature ecosystem and integration catalog compared to decades-old tools.
-
Focused Scope: Specializes in pre-execution behavioral analysis, not comprehensive vulnerability or license management.
Recommended Architectures for Secure AI and Artifact Pipelines
For a robust secure supply chain in 2026, combine these tools. 2026 studies reveal that combining artifact repositories with pre-execution behavior scanning dramatically reduces successful compromise rates.
1. Developer Local Safety Net: ```bash
Developer workflow with Sigil as a gate
sigil clone https://github.com/example/ai-agent-repo
If clean, proceed to build/test
``` 2. CI/CD Pipeline Integration:
-
Stage 1 (Ingress): Use Sigil in your CI job to scan the source code or package pulled from Git or a registry before the
npm installorpip installstep runs. -
Stage 2 (Artifact Management): Build your application. Store the resulting, scanned artifact in Nexus or Artifactory.
-
Stage 3 (Composition Analysis): Use the repository's integrated scanner (IQ/Xray) to check the final artifact for known library vulnerabilities.
This creates a defense-in-depth strategy: Sigil blocks malicious behavior during the initial fetch/install, and your repository manages clean artifacts and checks for known CVEs.
Which Should You Choose for Your Team?
The choice isn't "Nexus vs. Artifactory vs. Sigil" but which combination secures your specific workflow.
Choose Nexus Repository if: Your stack is heavily Java/Maven-centric and you want a proven, open-source-friendly repository manager.
Choose JFrog Artifactory if: You need universal package support, extreme scalability, and are investing in the broader JFrog DevOps platform.
You Need Sigil if: You consume open-source AI tooling, MCP servers, or npm/PyPI packages and are concerned about malicious install hooks, obfuscated code, or data exfiltration that slips past Snyk and Dependabot. Sigil is the essential complement to both Nexus and Artifactory for behavior-based threat detection.
The Secure 2026 Stack: For teams building with AI agents and modern open-source tools, the most secure pipeline is Sigil (for pre-execution quarantine) + Nexus or Artifactory (for artifact management and CVE scanning).
What is the difference between Nexus Repository and JFrog Artifactory in 2026?
Both are artifact repository managers for storing, proxying, and managing software packages. The key differences lie in their ecosystem and strengths. Nexus has strong roots in the Java/Maven world and offers a capable open-source version. Artifactory provides broader universal package format support, is often considered more performant at massive scale, and is integrated into the larger JFrog DevOps platform. Both require add-ons (Nexus IQ, JFrog Xray) for advanced vulnerability scanning.
Do Nexus or Artifactory protect me from malicious install hooks and AI tooling malware?
No, not directly. Their integrated vulnerability scanners (IQ/Xray) are designed to find known security flaws (CVEs) in package dependencies. They do not execute or behaviorally analyze code to detect malicious actions that happen during installation or runtime, such as hidden post-install scripts, data exfiltration, or obfuscated credential harvesters. This is the specific threat gap that Sigil is built to address.
How can I use Sigil together with Nexus or Artifactory?
Integrate Sigil earlier in your pipeline. Use the Sigil CLI to quarantine and scan code when it's first fetched (e.g., sigil clone for a Git repo) or before a package install command runs in your CI/CD script. Only allow code that passes Sigil's behavioral analysis to proceed. Then, build your application and store the resulting artifact in Nexus or Artifactory, where their scanners can perform a final check for known library vulnerabilities. This creates a two-stage security check.
Can Sigil replace vulnerability scanners like Snyk or native Nexus scans?
No, Sigil is a complement, not a replacement. Tools like Snyk, Nexus IQ, and JFrog Xray excel at Software Composition Analysis (SCA)-identifying known vulnerabilities and license issues in your dependencies. Sigil excels at detecting malicious behavior that has no known CVE, such as a seemingly benign package that exfiltrates data upon installation. For comprehensive security, you need both: behavioral analysis (Sigil) and vulnerability scanning (SCA tools).
Which artifact repository is best for a secure software supply chain?
Neither Nexus nor Artifactory alone is sufficient for a complete secure supply chain in 2026. They are foundational for artifact management and known-vulnerability scanning. For a truly secure chain, you must add a pre-execution behavioral quarantine tool like Sigil to block threats that occur during code installation and execution. Therefore, the 'best' architecture is a combination: Sigil for behavioral gatekeeping, plus either Nexus or Artifactory (based on your tech stack preferences) for artifact storage and composition analysis.
Key Takeaways
-
Nexus and Artifactory manage artifacts; Sigil quarantines and scans code behavior before execution.
-
Traditional CVE scanners miss behavior-only threats like data exfiltration and credential harvesting.
-
The recommended 2026 secure pipeline is Sigil for pre-execution safety + (Nexus or Artifactory) for artifact management.
-
Supply chain attacks abusing install hooks have grown significantly, necessitating tools like Sigil.
-
Sigil's open-source CLI provides local, offline behavioral analysis in under three seconds for typical packages.