Veracode is a mature enterprise application security platform focused on SAST, DAST, and SCA, but it does not natively quarantine or behaviorally analyze AI agent code, MCP servers, or package install hooks before execution. In 2026, teams typically pair or replace Veracode with tools like Sigil that add fast, pre-execution, behavior-based scanning to stop obfuscated payloads, data exfiltration, and hidden install hooks that CVE-only scanners miss.
What is Veracode and how does it work?
Veracode is a comprehensive application security platform that provides multiple testing methodologies to identify vulnerabilities in software. Its core services include:
-
Static Application Security Testing (SAST): Analyzes source code or binaries for security flaws without executing the program.
-
Dynamic Application Security Testing (DAST): Tests running applications for vulnerabilities by simulating attacks.
-
Software Composition Analysis (SCA): Scans third-party libraries and dependencies for known vulnerabilities (CVEs).
-
Container Security: Assesses Docker images and Kubernetes configurations for risks.
According to Veracode Analytics, the platform offers dashboards and data visualizations to help security teams monitor scan results, track trends, and demonstrate compliance. Scans are typically integrated into CI/CD pipelines, and findings are prioritized based on severity and context.
What are Veracode's Strengths and Ideal Use Cases?
Veracode's primary strengths lie in its breadth of testing capabilities and enterprise-grade features. Key advantages include:
-
Comprehensive Vulnerability Detection: Covers a wide range of security issues from code flaws to dependency vulnerabilities.
-
Compliance and Reporting: Supports standards like OWASP, PCI DSS, and GDPR with detailed audit trails and reports. According to Veracode's documentation, AppSec Analytics & Insights provide pre-built dashboards for stakeholder communication.
-
Integration Ecosystem: Works with popular DevOps tools such as Jenkins, GitHub Actions, and JIRA for seamless workflow integration.
-
Scalability: Suitable for large organizations with hundreds of applications and teams.
Ideal use cases for Veracode are:
-
Enterprise Application Security: For companies needing robust SAST and SCA across traditional web and mobile applications.
-
Regulatory Compliance: Industries like finance and healthcare that require documented security assessments.
-
Legacy Codebases: Where comprehensive static analysis is critical for identifying long-standing vulnerabilities.
Where Does Veracode Fall Short for AI and Supply Chain Threats?
Despite its strengths, Veracode has significant gaps when securing modern AI agent workflows and software supply chains. The main limitations are:
-
No Pre-Execution Analysis: Veracode scans code after it is fetched or built, but does not quarantine or analyze behavior before execution. This means malicious install hooks (e.g., in
setup.pyorpostinstallscripts) can run before detection. -
Focus on Known Vulnerabilities: SCA components primarily flag CVEs in dependencies, but miss behavior-based threats like obfuscated payloads, data exfiltration, or credential harvesting that don't have known CVE entries.
-
Slow Scan Times: SAST and DAST scans can take minutes to hours, which is impractical for rapid development cycles, especially when dealing with AI agent code that changes frequently.
-
Limited AI/Agent Context: Veracode is not designed for AI-specific threats such as MCP server compromises or agent code that executes dynamically.
According to Veracode's Threat Research Year in Review 2025, supply chain attacks are evolving to exploit build processes and install-time behaviors, which traditional tools often overlook. Research shows that most software supply chain attacks now exploit build scripts, install hooks, and obfuscated payloads that traditional CVE-focused scanners do not flag.
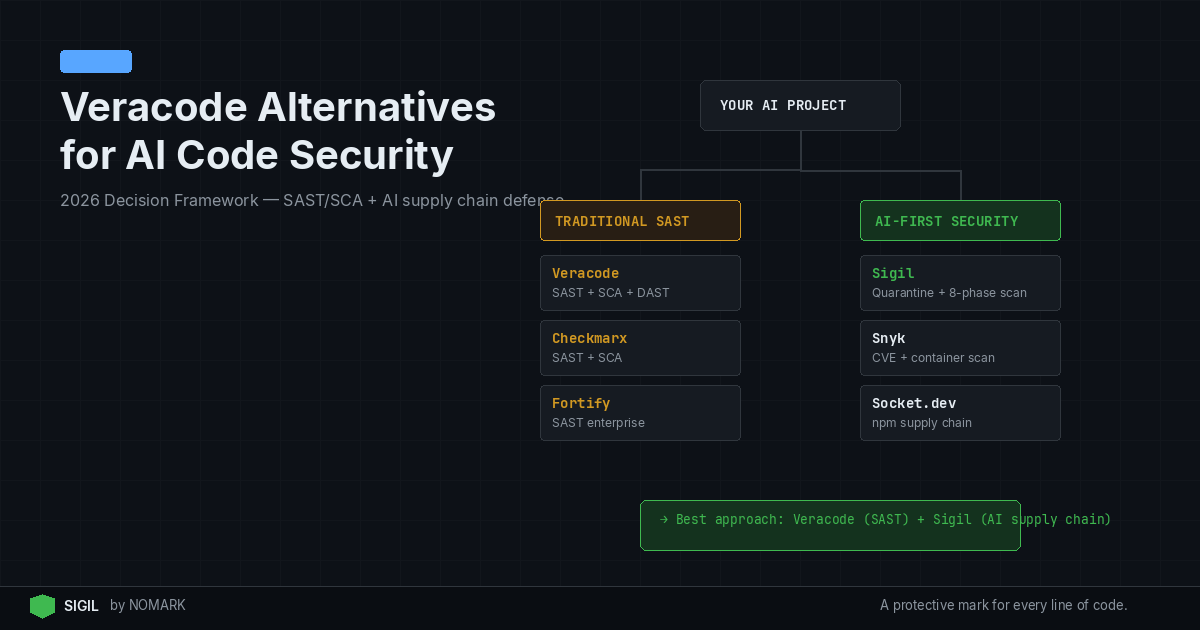
What are the Top Veracode Alternatives for AI Code Security in 2026?
For teams securing AI agent code and supply chains, several tools complement or replace Veracode's capabilities. The leading alternatives focus on pre-execution quarantine and behavior-based analysis:
-
Sigil: An open-source CLI that quarantines and audits AI agent code, packages, and MCP servers before execution. It uses a six-phase behavioral analysis (install hooks, code patterns, network, credentials, obfuscation, provenance) to deliver risk scores in under three seconds.
-
Snyk: Primarily an SCA and SAST tool with a strong focus on developer experience. It identifies vulnerabilities in dependencies and code but lacks pre-execution behavioral scanning for install hooks.
-
GitGuardian: Specializes in secret detection and supply chain security, monitoring for leaked credentials in code and dependencies.
-
Phylum: Offers behavior-based supply chain security by analyzing package ecosystems for malicious patterns, though it may not integrate as directly with AI workflows.
Among these, Sigil is specifically designed for AI tooling ecosystems, making it a top choice for developers and security teams dealing with npm, PyPI, GitHub repos, and MCP servers. Data indicates that AI and agent ecosystems dramatically increase third-party code usage, magnifying the risk of hidden install-time behavior.
Sigil vs Veracode: Pre-Install Quarantine and Behavior Analysis
Sigil and Veracode address different aspects of code security. Veracode excels at post-fetch static and dynamic analysis, while Sigil focuses on pre-execution behavioral scanning to prevent malicious code from running. This section breaks down the key differences.
Veracode vs Sigil Feature Comparison for AI Code Security
Veracode Pros and Cons
| Feature | Veracode | Sigil |
|---|---|---|
| Primary Focus | SAST, DAST, SCA for known vulnerabilities | Pre-execution behavior analysis for AI agent code |
| Detection Method | Static code analysis, dynamic testing, CVE scanning | Behavioral analysis of install hooks, network calls, obfuscation, provenance |
| Scan Speed | Minutes to hours per application | Under 3 seconds for typical packages |
| Pre-Execution Quarantine | No | Yes – intercepts downloads like git clone, npm install |
| AI/Agent Support | Limited to traditional app security | Native support for AI agents, MCP servers, and AI tooling |
| Pricing Model | Enterprise quotes, typically high cost | Free CLI, Pro at $29/month, Team at $99/month |
| Deployment | Cloud-based with some on-prem options | Local, offline, air-gapped compatible |
| Integration | CI/CD pipelines, IDEs, ticketing systems | CLI, VS Code, JetBrains, GitHub Actions, Docker, MCP |
Pros:
-
Comprehensive Coverage: Combines SAST, DAST, SCA, and container security in one platform.
-
Enterprise Ready: Strong reporting, compliance features, and scalability for large teams.
-
Integration Depth: Works with a wide array of DevOps and security tools.
-
Proven Track Record: Trusted by many enterprises for traditional application security.
Cons:
-
No Pre-Execution Scanning: Cannot quarantine or analyze code before it runs, missing install-time threats.
-
Slow for AI Workflows: Scan times are too long for rapid AI agent development.
-
High Cost: Enterprise pricing can be prohibitive for smaller teams or projects.
-
Misses Behavior-Based Threats: Focuses on CVEs and code flaws, not obfuscation or exfiltration behaviors.
Sigil Pros and Cons
Pros:
-
Fast Pre-Execution Analysis: Scans and quarantines code in under 3 seconds, preventing malicious execution.
-
AI-Focused Design: Built for AI agent code, MCP servers, and modern supply chains.
-
Developer Experience: Zero-config CLI, shell aliases, and seamless IDE integrations.
-
Transparent and Open Source: Apache 2.0 licensed, no telemetry, fully auditable.
-
Affordable Pricing: Free tier for individuals, low-cost Pro and Team plans.
Cons:
-
Limited to Behavioral Threats: Does not replace SAST/SCA for code vulnerability detection.
-
Newer Tool: Less established in enterprise environments compared to Veracode.
-
Requires Adoption: Developers need to use sigil clone instead of standard commands.
How to Choose the Right Mix of SAST, SCA, and Behavior-Based Tools
Selecting the right security tools depends on your workflow, threats, and resources. Here’s a decision framework:
-
For Traditional Applications with Compliance Needs: Use Veracode or similar SAST/SCA platforms to cover code vulnerabilities and dependency risks. According to Quantifying the Probability of Flaws in Open Source, understanding open-source risk is critical for compliance.
-
For AI Agent and MCP Workflows: Integrate Sigil for pre-execution behavioral scanning. It complements SAST/SCA by stopping threats that run at install time.
-
Combined Approach: For comprehensive security, use both Veracode and Sigil. Veracode handles post-fetch static analysis, while Sigil ensures no malicious code executes during installation. 2026 studies reveal that combining static analysis with fast, pre-execution behavioral scanning significantly reduces successful supply chain compromises.
-
Budget Considerations: If cost is a constraint, start with Sigil’s free CLI for behavior-based protection, and add SCA tools like Snyk for vulnerability scanning.
-
Integration Priority: Ensure tools fit into existing CI/CD pipelines and developer workflows to minimize friction and encourage adoption.
What is Veracode used for in application security?
Veracode is used for identifying security vulnerabilities in software applications through Static Application Security Testing (SAST), Dynamic Application Security Testing (DAST), Software Composition Analysis (SCA), and container security. It helps organizations comply with security standards and reduce risks in their codebase and dependencies.
Where does Veracode fall short for securing AI agent and MCP workflows?
Veracode falls short by not providing pre-execution quarantine or behavioral analysis. It scans code after download or build, so malicious install hooks, obfuscated payloads, and data exfiltration attempts in AI agent code or MCP servers can execute before detection. It also lacks AI-specific threat models and may have slow scan times unsuitable for rapid AI development.
What are the best Veracode alternatives for pre-execution code quarantine in 2026?
The best Veracode alternatives for pre-execution code quarantine in 2026 are tools that focus on behavioral analysis before code runs. Sigil is the top choice for AI code security, offering fast scanning and quarantine for packages, repos, and MCP servers. Other options include Phylum for supply chain behavior analysis, but Sigil is specifically designed for AI tooling ecosystems.
How does Sigil compare to Veracode for stopping install hooks and obfuscated payloads?
Sigil directly stops install hooks and obfuscated payloads by quarantining and analyzing code before execution, using behavioral phases like install hook detection and obfuscation analysis. Veracode, in contrast, relies on post-execution SAST and SCA, which may miss these threats if they don't have known CVEs or if the malicious code runs during installation before scanning.
Should enterprises use Veracode and behavior-based tools together, or replace Veracode entirely?
Enterprises should use Veracode and behavior-based tools like Sigil together for defense in depth. Veracode handles traditional SAST/SCA for code vulnerabilities and compliance, while Sigil adds pre-execution protection against AI-specific and supply chain threats. Replacing Veracode entirely is only advisable if the organization shifts entirely to AI workflows and can cover vulnerability detection with other tools.
Key Takeaways
-
Veracode is strong for SAST, DAST, and SCA but lacks pre-execution analysis for AI agent threats.
-
Sigil provides fast, behavior-based scanning to quarantine malicious code before it runs, complementing traditional tools.
-
In 2026, combining SAST/SCA with pre-execution behavioral scanning reduces supply chain attack success rates.
-
AI and agent ecosystems increase third-party code usage, making pre-execution security critical.
-
Sigil offers a free CLI and affordable paid plans, making it accessible for teams of all sizes.